How Does a Password Get Hacked
Did you know that cybercriminals attempt to gain access to websites by executing over 280 million malicious login attacks each day? While they might not have an exact 50% daily success rate (or even close), countless personal information records are lost to hackers each year.
These numbers are enough to make any businessman want to tighten his online operations to avoid data breaches. Here's everything you should know about preventing password hacks
How Do Hackers Get Your Password?
Hackers use a variety of methods to guess passwords. The easiest way to get sensitive information is to purchase it from the dark web.
Another method involves using sophisticated software programs to guess password combinations. Many times, this can be done within minutes because most people use weak passwords. These programs include:
- Dictionary Attack – where a list of predetermined passwords is used to guess your username/password combination.
- Brute force attack – this generates a combination of symbols, letters, and numbers until it hits your password
- Phishing - involves tricking or pressuring people into giving them their personal information (such as email addresses).
What Can Happen If Your Password Gets Hacked
To start with, if hackers gain access to your password, they could use your login details to access your accounts. Hackers can change passwords and prevent people from logging into their hijacked accounts, especially if they include any payment details. This is known as account takeover.
Cybercriminals can steal identities by using stolen passwords. They can then commit fraud by taking out loans in the victim's name, using their credit cards, or gaining other benefits at their expense.
Your data can also be used by others for their own purposes. Stolen personal information may also be used to trick unwitting company employees into handing over confidential information that could cause damage to the company.
The Risk of Using the Same Password for Different Apps
Imagine having one key for everything you need unlocked. If someone copies your keys, every single door you use becomes open to them. That's exactly what happens when you use just one password for multiple accounts or apps.
If a hacker successfully breaks into your account on one site, they might use the same credentials to break into your accounts on other sites. If you use the same password for every account, then your entire digital life could be at risk.
As it is not safe to reuse passwords across multiple websites, experts do not recommend doing so. If hackers can use powerful software tools to break through so-called "strong" passwords, it shouldn't be too hard for them to guess a weak password, or any variations of it, in just a few seconds.
Using a Password Manager
However, how do you memorize so many different passwords if you have multiple online accounts? Remembering just one strong, unique password is how.
You don't need to remember all your different passwords for all your various online accounts. A password manager can help you manage them all at once. A password manager is an application that stores and manages passwords for you.
Beyond simply encrypting user passwords, Password Safe can generate complex passwords and then fill them into required fields on web pages, email clients, and even local applications. That way, you won't need to remember multiple passwords but only one master password instead.
How Secure is Your Password?
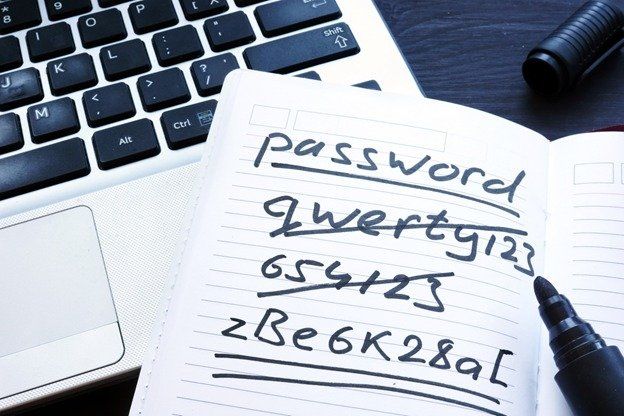
Experts suggest making sure your passwords are at least 12 to 16 characters long so they're hard to guess. It should also include both upper- and lowercase letters, numbers, and symbols Here is an example for a more complicated password:
- my$funzp04JMT+do41!
- 8yadgal$%$IT38gaM!4y#
- 9dr@gFun3!mkl&IT!
Passwords that contain your name, date of birth or any other personal details can be easily guessed and cracked. Don't use sequential numbers, letters, or common substitutions. Here are some examples of weak passwords:
- password1
- john1980
- 2021abcsecretreportxyz
Safely Sharing Passwords with Your Team

Sharing of passwords isn't totally ruled out even when working with a team. However, since humans are the weakest link when it comes to cybersecurity, it is important to look for ways to securely share passwords without putting your company at risk.
There are three ways to do this.
- Share passwords verbally: It is best if this is done face to face in a secured setting. If that isn't possible, maybe because your team works remotely you could use some sort of secure communication method.
- Use a password vault: A password vault is an application that lets you store data securely in a single file. It can be used to keep records, such as addresses, usernames and passwords. A password vault is an encrypted file that stores passwords for websites and applications. Store sensitive pieces of information in an encrypted password vault and share them with your team.
- Share passwords through encrypted emails: Do not communicate passwords through regular or unencrypted emails for any reason. If neither option 1 nor option 2 is feasible, make sure you send an encrypted email. Research some of the trustworthy open source encryption tools for this purpose
What to Do When an Employee Leaves
Sharing passwords with your team members is one of the biggest security risks. If someone leaves the company, they could steal your password database. It’s especially important when someone leaves because he/she has been fired or is a greedy techie.
Here are some things that you can do if someone leaves your team:
- Set up two-factor authentication: Two-factor or multi-factor authentication provides an extra layer of digital security. Electronic authentication requires users to provide multiple pieces of evidence before gaining full access to an account, application, or website. Two-factor authentication is best implemented well ahead of time, even for employees who don't need access to sensitive business systems.
- Create password levels: Everyone on a team can have access to a level 1 password. If there are multiple levels of access, passwords for more sensitive user accounts should only be given to higher-level managers.
If you use a password manager though, all your logins are stored in one place. It allows for easier access by employees based on their job titles or specific roles. You can easily see who has access to which accounts or applications. If an employee leaves, it's easier to change their passwords for every site and application they've ever logged into.